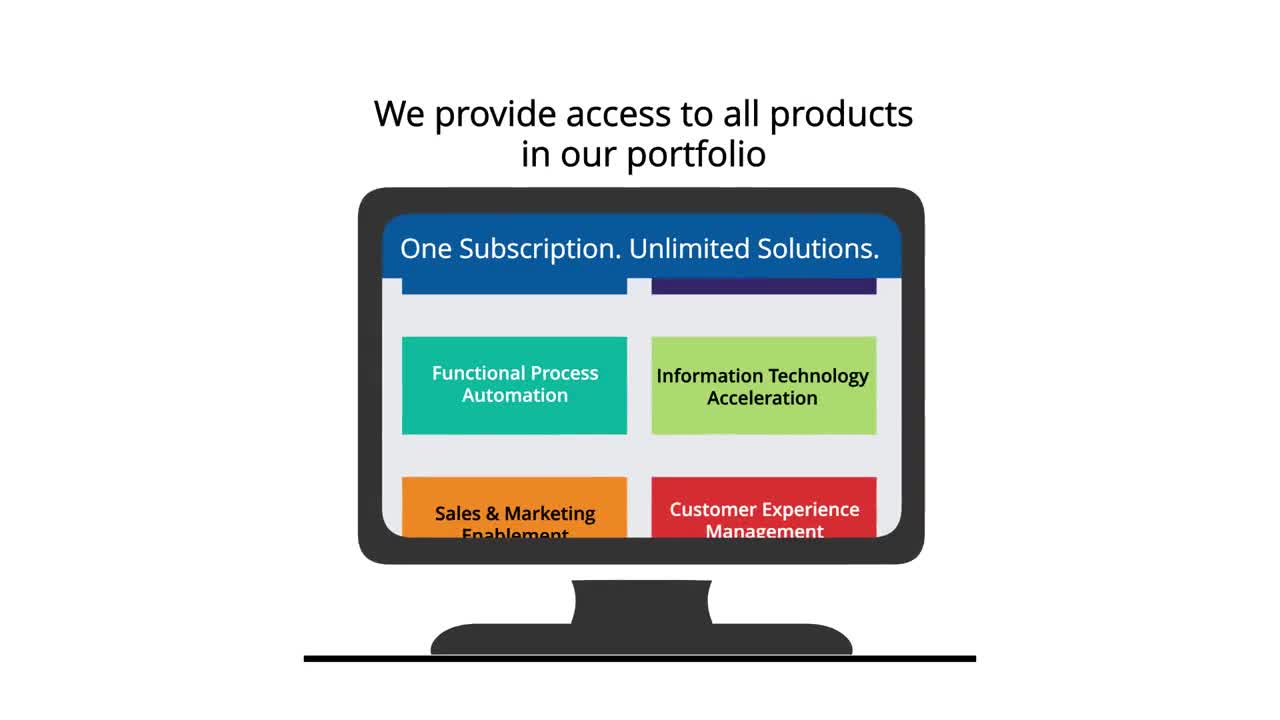
FUNCTIONAL PROCESS AUTOMATION
Manage and drive your business across all operational functions, including Finance, HR, Compliance, Procurement and more.
Solutions in the Functional Process Automation Suite help you reduce operating costs while improving quality.
INFORMATION TECHNOLOGY ACCELERATION
Accelerate apps and infrastructure for digital success.
Solutions in the Information Technology Acceleration Suite help you manage your IT environment, save costs and leverage massive data stores.
COMMUNICATIONS & REMOTE ENGAGEMENT
Keep your distributed employees and executives well-connected and engaged.
Solutions in the Communications & Remote Engagement Suite help you communicate internally from emergency alerts to market insights and everyday collaboration.
COMMERCE & DIGITAL ENGAGEMENT
Optimize your customers' journey — to accelerate online selling and servicing.
Solutions in the Commerce & Digital Engagement Suite help you provide exceptional customer service, manage commerce across a variety of platforms and deliver personalized content.
CUSTOMER EXPERIENCE MANAGEMENT
Measure, understand, influence and engage customers and target audiences across your business.
Solutions in the Customer Experience Management Suite help you collect customer experience data, manage customer requests and provide delightful customer interactions.
SALES & MARKETING ENABLEMENT
Win more deals & close deals faster by arming teams with critical insights to target highest potential leads and improve pipeline velocity.
Solutions in the Sales & Marketing Enablement Suite help you maximize your sales and marketing teams' efficiency with just-in-time market intelligence, predictive lead scoring and more.